Author: Alan Tobagua
-
But Can They Hack?: ExaminingTechnological Proficiency in the US Far Right Tom Holt
Research surrounding radicalization to and use of violence among extremist and terror groups has expanded over the last decade. These studies have improved our understanding of the potential process of radicalization and identified differences between lone wolf and group-based extremist threats. There are still fundamental questions that must be addressed, particularly regarding the role of the Internet in radicalization and recruitment as well as general technological skill of extremist groups. Few studies have considered this issue, especially among Far Right groups which have been identified as one of the top threats to public safety within the United States. This exploratory study addresses these issues using a comparative analysis of threads from multiple widely-used web forums in the U.S. dedicated to the white nationalist and white power movement. The findings demonstrate that there are distinct differences in the nature of conversations within these sites, particularly in their use of radical or race-based messages and their proficiencies with technology generally. The implications of this study for computer security professionals and the intelligence community will be examined in depth. -
How to find the JETPLOW on Cisco firewalls installed
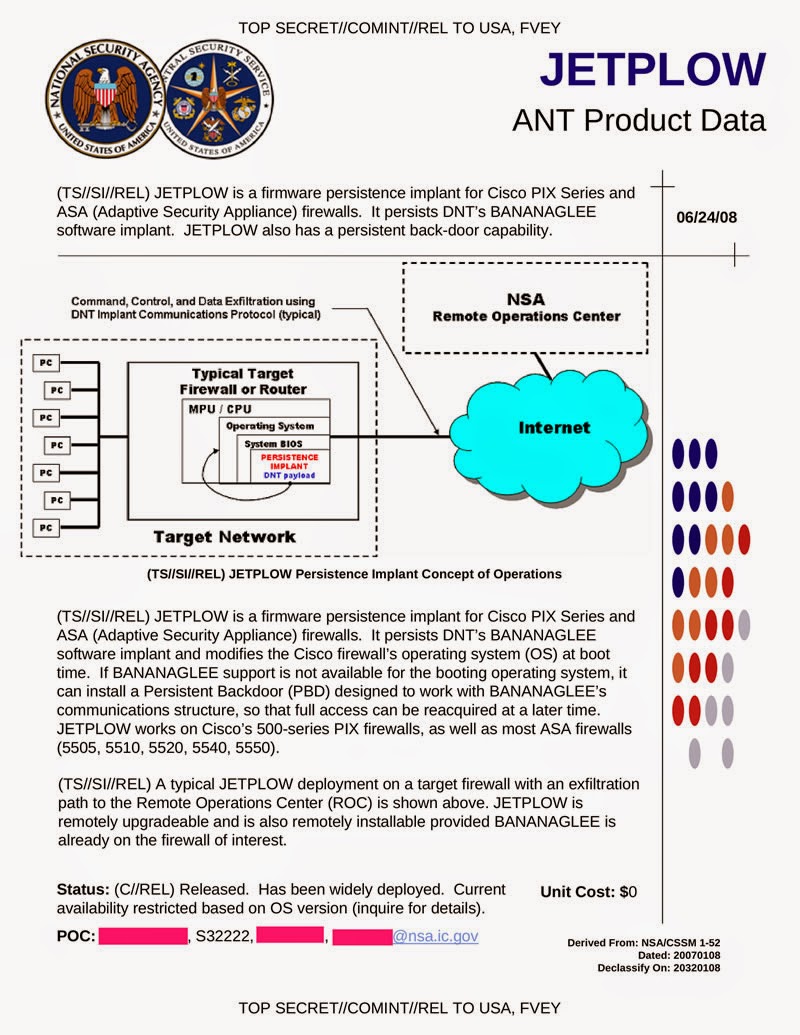
JETPLOW is a firmware persistence implant for Cisco PIX Series and ASA (Adaptive Security Appliance) firewalls. It persists DNT’s BANANAGLEE software implant. JETPLOW also has a persistent back-door capability.JETPLOW is a firmware persistence implant for Cisco PIX Series and ASA (Adaptive Security Appliance) firewalls. It persists DNT’s BANANAGLEE software implant and modifies the Cisco firewall’s operating system (OS) at boot time. If BANANAGLEE support is not available for the booting operating system, it can install a Persistent Backdoor (PDB) designed to work with BANANAGLEE’S communications structure, so that full access can be reacquired at a later time. JETPLOW works on Cisco’s 500-series PIX firewalls, as well as most ASA firewalls (5505, 5510, 5520, 5540, 5550).
A typical JETPLOW deployment on a target firewall with an exfiltration path to the Remote Operations Center (ROC) is shown above. JETPLOW is remotely upgradable and is also remotely installable provided BANANAGLEE is already on the firewall of interest.
Status: Released. Has been widely deployed. Current availability restricted based on OS version (inquire for details).
-

Why the Russian Hackers strikes back
The Russian Federation holds an interesting, albeit a dubious position in the ranks of nation state cyber-actors. While ranked third among countries in terms of volume of cyber activity (behind the U.S. and China, according to Deutsche Telekom’s honeypot network data), Russia is widely regarded as a having the most sophisticated and skilled hackers.Unlike the Chinese government which employs thousands of hackers in the People’s Liberation Army, the Russian government’s relationship with resident hackers is much murkier. The trails to cyber-attacks originating in Russia tend to end at civilian hacktivist groups and criminal organizations, perhaps providing officials with plausible deniability. This may suggest an implicit support for criminal hackers in Russia, given government’s notorious reputation as being inherently corrupt.
Given the highly publicized industry hacks attributed to Russian entities, it’s easy to conclude that the government’s motivation behind hacking is directly related to financial gain. But that conclusion is, perhaps, somewhat simplistic. As an alternative, consider viewing Russian hacking through the prism of geo-politics. It is feasible that the Russian government has established an iniquitous partnership with Russian civilian hackers to achieve geo-political goals. It may not be possible to know with certainty what motivates the government to participate in nefarious cyber activity, but it’s equally conceivable that Russian officials views hacking, or more appropriately cyber warfare, as a political tool which, when employed, is extremely effective at helping a nation state achieve a geopolitical goal.
The notion that the Russian government is willing to use the cyber domain as a political, if not military, arena is not new. Recall the cyber-attacks alleged to have been orchestrated by the Russian Government during the 2008 Russo-Georgian War, a war considered by some to be the first cyber-war. Post war analysis suggests that the Russian Government leveraged the vast network of civilian cyber actors, including organized crime organizations, to conduct the attacks. The military significance of the cyber-targets attacked during the war, and the synchronization of the attacks with Russian military operations may be too coincidental to reasonably conclude Russian civilian hackers were acting autonomously.
In December 2014, the German Federal Office for Information Security (BSI) disclosed that a cyber-attack was executed on a steel plant, resulting in the abnormal shut down of a large blast furnace and associated systems. The BSI report characterized the attackers as highly skilled, and that they used social engineering and extensive knowledge of the network to circumvent security and specialized software designed to prevent such attacks. It is difficult to identify with certainty the parties responsible for these attacks, but the timing of diplomatic talks between the Ukraine and Germany point toward the Russian government. This cyber-attack is significant because it signals an escalation in tactics, a willingness to create physical damage to infrastructure.
More recently, the shutdown of German Government websites, which overlapped with a scheduled meeting this month between German President Joachim Gauck and Ukrainian Prime minister Arsney Yatseniuk, strongly suggests a connection between cyber operations conducted by Russian hacker groups and Russian politicos. The Russian hacktivist group, CyberBerkut, claimed responsibility for the attacks and demanded the Germans withdraw support for Ukraine. We can’t be certain that CyberBerkut was sponsored by the Russian government, but the timing of the cyber attacks with Russian activity in the Ukraine is compelling.
The renowned German military theorist Carl von-Clausewitz believed war to be a political instrument, and we can easily extrapolate Clausewitz’ thought to cyberwar in a modern context. With that point in mind, the Russian government has applied Clausewitz’ theories to achieve national political goals by leveraging an increasingly sophisticated hacker population. While the U.S. and many of her allies grapple with the implications of conducting offensive cyber operations, the Russian Government is writing the first book on geopolitics and global cyber warfare.
-

За что АНБ доплачивает инженерам электросвязи Укртелекома
В эти дни в Ганновере проходит крупнейшая компьютерная выставка CeBIT. Перед полным залом IT-специалистов на CeBIT Global Conferences выступил Эдвард Сноуден по видеосвязи из Москвы. И предупредил инженеров электросвязи об опасности.По его словам, именно представители сферы IT — главная цель АНБ, а вовсе не журналисты, политики или дипломаты. «Они ищут людей, у которых есть доступ к инфраструктуре, администраторов, инженеров, работников сервис-провайдеров, — сказал Сноуден. — Они ищут вас не потому, что вы террористы или подозреваемые, а потому, что у вас есть доступ к инфраструктуре, к конфиденциальным записям, к частной жизни людей».Слова Сноудена не лишены смысла. Его собственный пример показывает, что рядовой технический сотрудник АНБ имеет доступ чуть ли не ко всей секретной информации, которая есть в наличии.
То же самое наблюдается в других государственных и частных организациях. У рядового сисадмина прав и полномочий в системе больше, чем у старшего менеджмента. Через технического инженера можно получить полный доступ, узнать все пароли и найти любые документы.
Неудивительно, что в последнее время повысился интерес к айтишникам не только со стороны АНБ, но и со стороны обычных преступных группировок.
Может быть, при такой профессиональной угрозе IT-специалистам нужно повысить зарплату и приставить к ним личных телохранителей?