One such analyst working on foreign soil started surveillance on nine phone numbers belonging to women over five years, from 1998 to 2003. He “listened to collected phone conversations,” according to a letter from the NSA’s Inspector General to Senator Charles Grassley released today. The unnamed spy conducted “call chaining” on one of the numbers — to determine who had called, or been called from, the phone — and then started surveillance on two of those numbers as well.
Author: Lallora
-
12 True Tales from Gen Keith Alexander about Creepy NSA Cyberstalking
The NSA has released some details of 12 incidents in which analysts used their access to America’s high-tech surveillance infrastructure to spy on girlfriends, boyfriends, and random people they met in social settings. It’s a fascinating look at what happens when the impulse that drives average netizens to look up long-ago ex-lovers on Facebook is mated with the power to fire up a wiretap with a few keystrokes.He was thwarted only after a woman he was sleeping with reported her suspicions that the analyst had been listening to her phone calls. The analyst resigned.In 2011, another civilian NSA employee abroad “tasked” the telephone number of her boyfriend and other foreign nationals. When she was asked about it, she claimed it was her practice to query the phone numbers of people she met socially to make sure she wasn’t talking to “shady characters.” (Because you wouldn’t want that.)In 2005, a military member used his first day of access to run six e-mail addresses belonging to an ex-girlfriend.Some of the abuses were referred to the Department of Justice, but none resulted in prosecution. The complete letter to Grassley follows. -
How to build the BGP UPDATE packet
bgp-update-create is a small program used to generate the payload of a BGP UPDATE message. It was written to test if routes could be injected in a BGP conversation between two routers.It’s usage is very simple; it takes three parameters:
–as: Autonomous System number
–nexthop: Host name or IP address of next hop
–destnet: Network number/prefix to advertise
To use it with tcphijack you just pipe its output to tcphijack, like in:
sudo bgp-update-create –as 2 –nexthop 1.1.1.1 –destnet 2.2.2.2 | tcphijack […]
or just send its output to a file and then use tcphijack’s -P switch to specify a payload:
bgp-update-create –as 2 –nexthop 1.1.1.1 –destnet 2.2.2.2 > payload.dat
sudo tcphijack […] -P payload.dat
bgp-update-create is built at the same time as tcphijack (by typing “make”), the header files used by bgp-update-create.c come from the Zebra project.
BGP Update Create download
-

Cyprus local Cisco Networking Academy
CCNA Exploration on Cyprus offers in-depth theory, challenging labs, and a detailed overview of protocol operations. It is designed for students with advanced problem-solving and analytical skills, such as degree candidates in engineering, mathematics, or science, or for working professionals who would like to advance their careers or gain certificationThe Cisco CCNA Exploration curriculum provides a comprehensive overview of networking; from fundamentals to advanced applications and services, while providing opportunities for hands-on practical experience and soft-skills development.
The curriculum teaches networking based on technology, covering networking concepts using a top-down, theoretical, and integrated approach – from network applications to the network protocols and services provided to those applications by the lower layers of the network. In addition, it offers a comprehensive and theoretical learning experience for analytical students, and uses language that aligns well with engineering concepts. Interactive activities are embedded in the curriculum, along with detailed, theoretical content. Advanced labs build critical thinking and problem solving skills and encourage exploration and research.
As Cisco states “Cisco Networking Academy delivers a comprehensive, 21st century learning experience to help students develop the foundational ICT skills needed to design, build, and manage networks, along with career skills such as problem solving, collaboration, and critical thinking. Students complete hands-on learning activities and network simulations to develop practical skills that will help them fill a growing need for networking professionals around the world. -
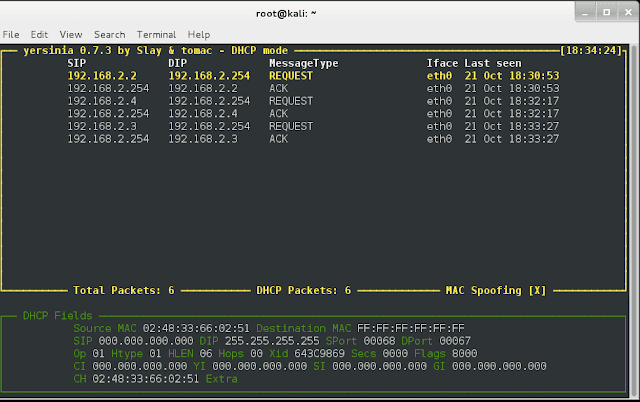
Yersinia is the best network Layer 2 hacking tool
It’s really hard to beat layer 2 hacking to really mess stuff up. While folks are up at layer 4-7 messin’ around with this socket or that scripting vuln, I am down here at layer 2 all fat, dumb and… fat.Now most folks have pushed layer two security off to the side as a internal LAN based attack and look to features like Dynamic ARP Inspection, IP Source Guard, Root Guard, etc to render these attacks as useless as meat thermometer at a vegan dinner. But with the massive spread of MPLS, Ethernet is being pushed to levels it was never really designed to be at. Layer 2 attacks are now as cool as the Fonz leaning against a 57 Chevy.For example, I run a peer based security research lab here in Wisconsin. Me and about five other security folks around the world run sensors and try to hack into each others networks for practice, out right humiliation and of course beer bounties. Sitting in Milwaukee Wisconsin working on a Newcastle and a slow burning Rocky Patal 1990 Vintage after the family went to bed, I started working on hacking a peer of mines network. Knowing we both had MPLS trunks at the PE, I guessed they may be passing PDU’s in what is know as full transparency mode. I started up a simple ARP spoof and sure enough I was the default gateway for my friends traffic in Ottawa. Man that is really something to run these LAN type of attacks on the wide side.For these types of attacks, it is really hard to beat to the tool Yersinia. http://www.yersinia.net/ if you are running the BackTrack ISO, Yersinia is already compiled and ready to go, so skip on down a few steps, if not, let’s just make this easy and say you are using Ubuntu. To install Yersinia, just open up a terminal and type:apt-get install yersiniaUsing Yersinia is a simple as ******* on a airplane and blaming it on someone else. Yersinia is wrote in C and is multithreaded so more then one person can use it and more then one attack can be launched. Yersinia runs in one of three modes which are invoked at the command line:– yersinia -I is the Interactive mode. This is a ncurses graphical interface that will take you back to the editing autoexec files in the DOS days of old. This is the most popular mode for Yersinia. Once you are here, notice at the top of the screen, it tells you what protocol mode it is in. The default is STP. Press the “h” key for help. The most important keys to know at the start (besides h) are “g” to change protocol attack mode, “x” is the attack mode screen and “e” allows you to edit protocol fields. A mega cool plus is that the attack screen will tell you which attacks are DOS attacks so you don’t mess up and send the wrong one!– yersinia -D is the Daemon mode. This mode is really cool. It allows me to start yersinia on a Linux machine and access it with any other via Telnet. For example after the daemon is started, I attached on port 12000: telnet 192.168.1.100 12000 It is designed to emulate IOS to some extent, so you will see a log in screen, U: root P:root but like IOS the fun stuff is at enable mode so now type:enable the password here is tomac. At this mode, all options must be set by hand, so…
Step One: is to config up a outbound interface: set interface eth0
Step Two: run your attack (STP in this example) with the command: run stp 1
This has to be done for each attack package, each time. I recommend liberal use of the ? command to figure out some of the config options and attack packages. It works at all levels like IOS. For example if you what to know the Spanning Tree Protocol attack packages type: run stp ?
Step Three: Monitor your success or failure with the show command. Attacks will run until you stop them and that is done with the command: cancel all to turn them all off or you can just cancel a single attack with the attack name.– yersinia -G is the Final mode to run Yersinia in is the GTK graphical mode. While this is a nice looking point/click style of interface, it is a bit buggy and not used that much.Yersinia really offers up a nice attack package for layer two pen testers. Protocols like CDP,VTP,HSRP,DTP,DHCP,STP,802.1Q and X are all fair game. Yersinia has to be ran at root level and to go into interactive mode (yersinia -I) you have to be at full screen on the terminal.A couple of things I do not use Yersinia for:
– DHCP attacks. I think Goobler is better and offers more options
– VTP attacks on adding/removing VLANs do not seem to workTools like Yersinia never really go out of style. Misconfigs and fully transparent WAN PDU passing will always keep the dust knocked off of your layer 2 skills. Put good ole Yersinia to the test. It is easy to use and works VERY well!